Second Sha1-Hulud Wave Affects 25,000+ Repositories via npm Preinstall Credential Theft
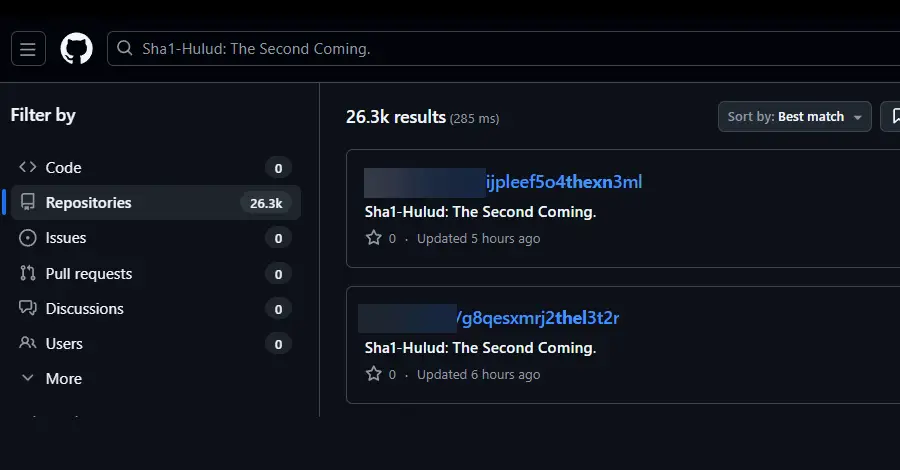
A second wave of coordinated attacks on the npm package registry has compromised hundreds of packages and affected over 25,000 repositories. The campaign, called Sha1-Hulud, exploits the npm preinstall phase to execute malicious code that steals credentials and secrets from developer machines.
Unlike the earlier Shai-Hulud attack from September, this variant is more sophisticated and destructive. It registers infected machines as GitHub self-hosted runners, extracts stored secrets and tokens (including npm, AWS, GCP, and Azure credentials), and uploads them to attacker-controlled repositories. The malware uses TruffleHog to scan for additional sensitive data.
The attack is notably more aggressive than its predecessor: if the malware fails to steal credentials or establish persistence, it triggers a wiper-like function that destroys the victim’s entire home directory—a shift from data theft to sabotage.
Security teams are advised to immediately identify and remove affected packages, rotate all credentials, and audit GitHub workflows for suspicious files or persistence mechanisms.
Leave a Reply