The Hacker NewsThe information technology (IT) workers associated with the Democratic People’s Republic of Korea (DPRK) are now applying to remote positions using real LinkedIn accounts of individuals they’re impersonating, marking a new escalation of the fraudulent scheme.
“These profiles often have verified workplace emails and identity badges, which DPRK operatives hope will make their fraudulentRead More
Author: chouaibcher@gmail.com
-

DPRK Operatives Impersonate Professionals on LinkedIn to Infiltrate Companies
-
Reynolds Ransomware Embeds BYOVD Driver to Disable EDR Security Tools
The Hacker NewsCybersecurity researchers have disclosed details of an emergent ransomware family dubbed Reynolds that comes embedded with a built-in bring your own vulnerable driver (BYOVD) component for defense evasion purposes within the ransomware payload itself.
BYOVD refers to an adversarial technique that abuses legitimate but flawed driver software to escalate privileges and disable Endpoint DetectionRead More -
Microsoft Discloses DNS-Based ClickFix Attack Using Nslookup for Malware Staging
The Hacker NewsMicrosoft has disclosed details of a new version of the ClickFix social engineering tactic in which the attackers trick unsuspecting users into running commands that carry out a Domain Name System (DNS) lookup to retrieve the next-stage payload.
Specifically, the attack relies on using the “nslookup” (short for nameserver lookup) command to execute a custom DNS lookup triggered via the Windows -

npm’s Update to Harden Their Supply Chain, and Points to Consider
The Hacker NewsIn December 2025, in response to the Sha1-Hulud incident, npm completed a major authentication overhaul intended to reduce supply-chain attacks. While the overhaul is a solid step forward, the changes don’t make npm projects immune from supply-chain attacks. npm is still susceptible to malware attacks – here’s what you need to know for a safer Node community.
Let’s start with the originalRead More -
Researchers Observe In-the-Wild Exploitation of BeyondTrust CVSS 9.9 Vulnerability
The Hacker NewsThreat actors have started to exploit a recently disclosed critical security flaw impacting BeyondTrust Remote Support (RS) and Privileged Remote Access (PRA) products, according to watchTowr.
“Overnight we observed first in-the-wild exploitation of BeyondTrust across our global sensors,” Ryan Dewhurst, head of threat intelligence at watchTowr, said in a post on X. “Attackers are abusingRead More -

Google Ties Suspected Russian Actor to CANFAIL Malware Attacks on Ukrainian Orgs
The Hacker NewsA previously undocumented threat actor has been attributed to attacks targeting Ukrainian organizations with malware known as CANFAIL.
Google Threat Intelligence Group (GTIG) described the hacking group as possibly affiliated with Russian intelligence services. The threat actor is assessed to have targeted defense, military, government, and energy organizations within the Ukrainian regional andRead More -
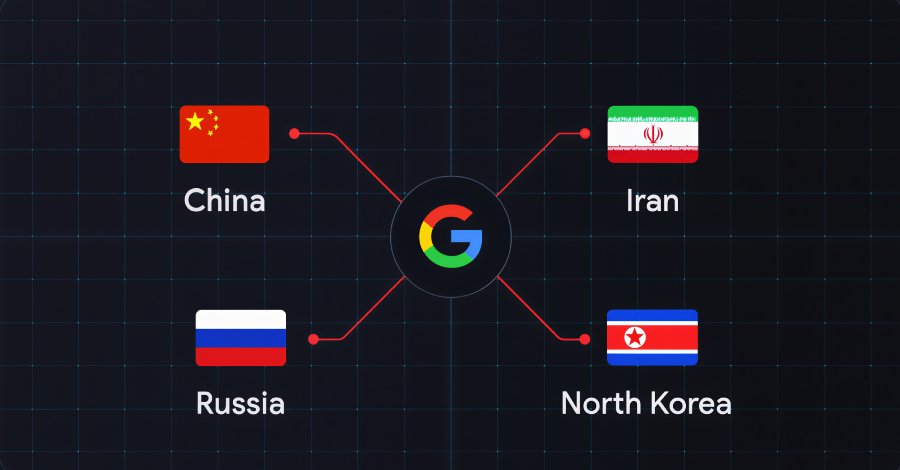
Google Links China, Iran, Russia, North Korea to Coordinated Defense Sector Cyber Operations
The Hacker NewsSeveral state-sponsored actors, hacktivist entities, and criminal groups from China, Iran, North Korea, and Russia have trained their sights on the defense industrial base (DIB) sector, according to findings from Google Threat Intelligence Group (GTIG).
The tech giant’s threat intelligence division said the adversarial targeting of the sector is centered around four key themes: striking defenseRead More -

UAT-9921 Deploys VoidLink Malware to Target Technology and Financial Sectors
The Hacker NewsA previously unknown threat actor tracked as UAT-9921 has been observed leveraging a new modular framework called VoidLink in its campaigns targeting the technology and financial services sectors, according to findings from Cisco Talos.
“This threat actor seems to have been active since 2019, although they have not necessarily used VoidLink over the duration of their activity,” researchers NickRead More -

Malicious Chrome Extensions Caught Stealing Business Data, Emails, and Browsing History
The Hacker NewsCybersecurity researchers have discovered a malicious Google Chrome extension that’s designed to steal data associated with Meta Business Suite and Facebook Business Manager.
The extension, named CL Suite by @CLMasters (ID: jkphinfhmfkckkcnifhjiplhfoiefffl), is marketed as a way to scrape Meta Business Suite data, remove verification pop-ups, and generate two-factor authentication (2FA) codes.Read More -
Webinar: Learn to Spot Risks and Patch Safely with Community-Maintained Tools
The Hacker NewsIf you’re using community tools like Chocolatey or Winget to keep systems updated, you’re not alone. These platforms are fast, flexible, and easy to work with—making them favorites for IT teams. But there’s a catch…
The very tools that make your job easier might also be the reason your systems are at risk.
These tools are run by the community. That means anyone can add or update packages. SomeRead More