The Hacker NewsIf you’re using community tools like Chocolatey or Winget to keep systems updated, you’re not alone. These platforms are fast, flexible, and easy to work with—making them favorites for IT teams. But there’s a catch…
The very tools that make your job easier might also be the reason your systems are at risk.
These tools are run by the community. That means anyone can add or update packages. SomeRead More
Category: Cybersecurity
Posts related to cyber threats, vulnerabilities, and security advisories
-
Webinar: Learn to Spot Risks and Patch Safely with Community-Maintained Tools
-

Chrome Extension Caught Injecting Hidden Solana Transfer Fees Into Raydium Swaps
The Hacker NewsCybersecurity researchers have discovered a new malicious extension on the Chrome Web Store that’s capable of injecting a stealthy Solana transfer into a swap transaction and transferring the funds to an attacker-controlled cryptocurrency wallet.
The extension, named Crypto Copilot, was first published by a user named “sjclark76” on May 7, 2024. The developer describes the browser add-on asRead More -

Shai-Hulud v2 Campaign Spreads From npm to Maven, Exposing Thousands of Secrets
The Hacker NewsThe second wave of the Shai-Hulud supply chain attack has spilled over to the Maven ecosystem after compromising more than 830 packages in the npm registry.
The Socket Research Team said it identified a Maven Central package named org.mvnpm:posthog-node:4.18.1 that embeds the same two components associated with Sha1-Hulud: the “setup_bun.js” loader and the main payload “bun_environment.js.”
“Read More -

Qilin Ransomware Turns South Korean MSP Breach Into 28-Victim ‘Korean Leaks’ Data Heist
The Hacker NewsSouth Korea’s financial sector has been targeted by what has been described as a sophisticated supply chain attack that led to the deployment of Qilin ransomware.
“This operation combined the capabilities of a major Ransomware-as-a-Service (RaaS) group, Qilin, with potential involvement from North Korean state-affiliated actors (Moonstone Sleet), leveraging Managed Service Provider (MSP)Read More -

When Your $2M Security Detection Fails: Can your SOC Save You?
The Hacker NewsEnterprises today are expected to have at least 6-8 detection tools, as detection is considered a standard investment and the first line of defense. Yet security leaders struggle to justify dedicating resources further down the alert lifecycle to their superiors.
As a result, most organizations’ security investments are asymmetrical, robust detection tools paired with an under-resourced SOC,Read More -

Sensitive Data Leaked: How Years of Online Formatter Use Exposed Passwords & API Keys
Organizations—including governments, telecoms, and critical infrastructure—have been unknowingly leaking passwords and sensitive credentials for years by pasting them into online code formatting tools like JSONFormatter and CodeBeautify. Recent research by watchTowr Labs uncovered over 80,000 files containing thousands of exposed secrets. This alarming trend highlights the urgent need for secure practices when handling code and credentials online. Stay vigilant and avoid pasting sensitive data into third-party tools.
-
Beware: Fake Windows Updates on Adult Sites Deliver Dangerous Malware
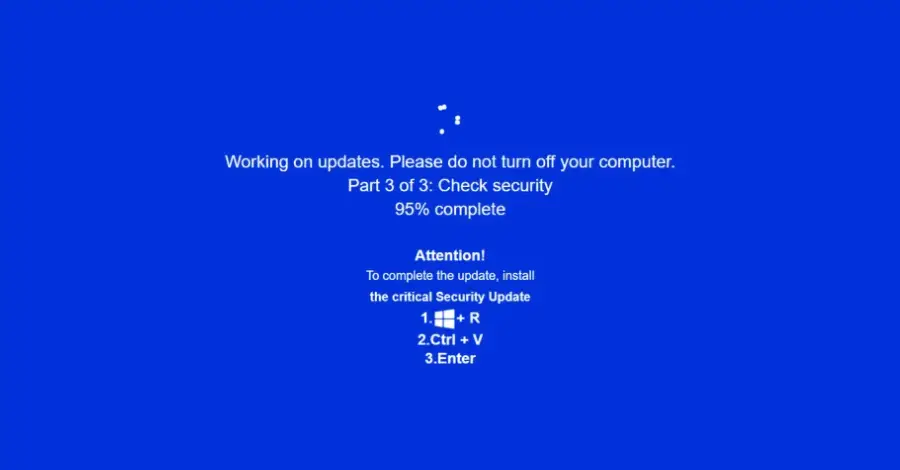
A new cyber campaign is tricking users with fake Windows update pop-ups on cloned adult websites. These convincing pop-ups, distributed via malvertising, lure victims into executing harmful commands that install multiple information-stealing malware strains. Researchers warn that these attacks are becoming more sophisticated and can compromise your personal data in seconds. Always verify update prompts and avoid downloading files from untrusted sources.
-
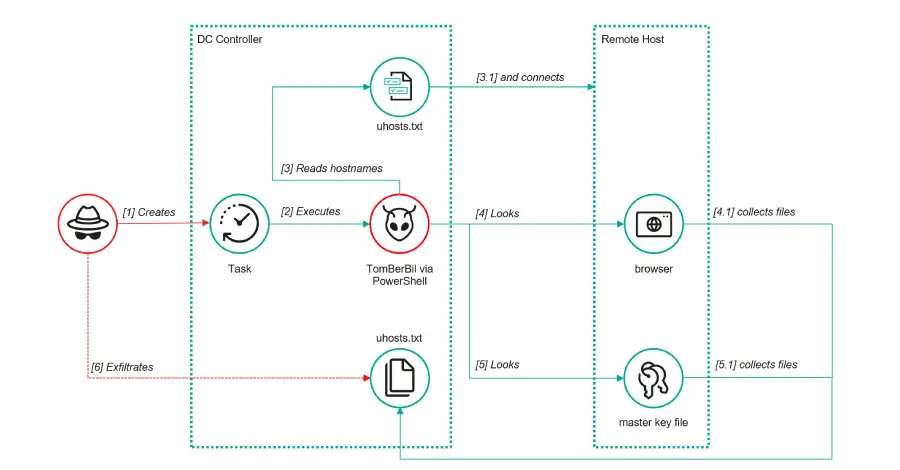
ToddyCat’s Advanced Hacking Tools Target Outlook and Microsoft 365 Accounts
The notorious hacker group ToddyCat is deploying new, stealthy tools to steal sensitive corporate emails and Microsoft 365 access tokens. Using a custom tool called TCSectorCopy, attackers can bypass security measures and gain direct access to confidential communications. This evolving threat demonstrates how quickly cybercriminals adapt their techniques, making robust email security and vigilant user awareness more critical than ever.
-

Top 3 SOC Challenges to Overcome Before 2026
As we approach 2026, cybersecurity is entering a new era. Threat actors are leveraging AI for smarter, more scalable attacks and hyper-realistic social engineering. Combined with global instability and rapid tech advancements, SOC teams face mounting challenges. To stay ahead, organizations must strengthen their defenses, embrace automation, and invest in continuous security training. Are you ready for the next wave of cyber threats?
-

Malicious Blender 3D Assets Used to Spread StealC V2 Malware
Cybercriminals are hijacking Blender 3D assets, embedding them with StealC V2 data-stealing malware. For at least six months, attackers have been distributing infected .blend files on popular platforms like CGTrader, putting unsuspecting designers and studios at risk. Always scan downloaded assets for malware and stay informed about the latest cyber threats targeting creative professionals.