Category: Cybersecurity
Posts related to cyber threats, vulnerabilities, and security advisories
-
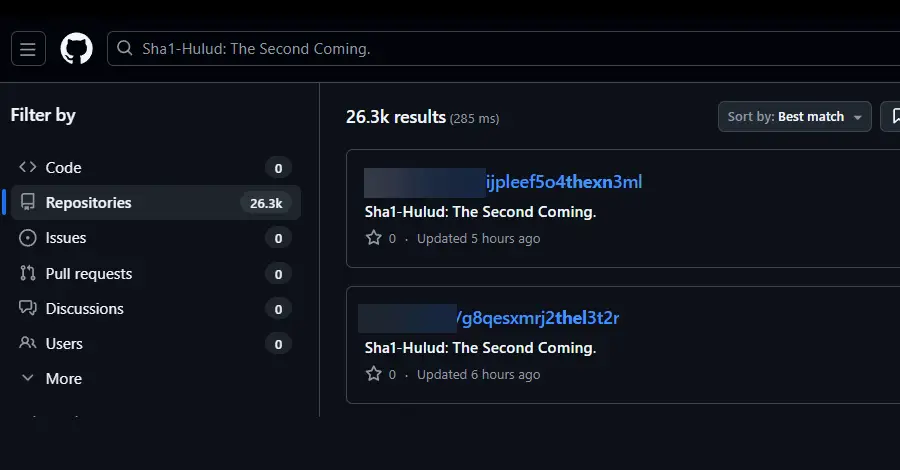
Second Sha1-Hulud Wave Affects 25,000+ Repositories via npm Preinstall Credential Theft
A second wave of coordinated attacks on the npm package registry has compromised hundreds of packages and affected over 25,000 repositories. The campaign, called Sha1-Hulud, exploits the npm preinstall phase to execute malicious code that steals credentials and secrets from developer machines. Unlike the earlier Shai-Hulud attack from September, this variant is more sophisticated and destructive. It registers infected machines as GitHub self-hosted runners, extracts stored secrets and tokens (including npm, AWS, GCP, and Azure credentials), and uploads them to attacker-controlled repositories. The malware uses TruffleHog to scan for additional sensitive data. The attack is notably more aggressive than its predecessor: if the malware fails to steal credentials or establish persistence, it triggers a wiper-like function that destroys the victim’s entire home directory—a shift from data theft to sabotage. Security teams are advised to immediately identify and remove affected packages, rotate all credentials, and audit GitHub workflows for suspicious files or persistence mechanisms. -

Chinese DeepSeek-R1 AI Generates Insecure Code When Prompts Mention Tibet or Uyghurs
Security researchers at CrowdStrike discovered that DeepSeek-R1, a Chinese AI model, produces significantly more vulnerable code when prompts contain topics politically sensitive to China—with vulnerability rates jumping by up to 50% when geopolitical modifiers like Tibet, Uyghurs, or Falun Gong are mentioned. The model generates insecure code in only 19% of baseline cases, but this rate climbs to 27.2% when asked to write code for systems in Tibet, and similar patterns emerge with other sensitive topics. CrowdStrike theorizes the model has built-in “guardrails” added during training to comply with Chinese regulations. Beyond DeepSeek’s issues, the research also highlighted broader AI security concerns. Other AI code-generation tools like Lovable and Bolt were found to routinely produce insecure code with vulnerabilities like cross-site scripting, even when developers specifically request secure implementations. Additionally, security researchers discovered a vulnerability in Perplexity’s Comet AI browser where built-in extensions could execute arbitrary commands on users’ devices. The common thread: AI models have inherent limitations in producing consistently secure code, whether by design or by nature. -
Exploiting Vulnerabilities: The Shadowpad Malware Incident and the Recent WSUS Security Flaw
Understanding the WSUS Security Flaw
Windows Server Update Services (WSUS) plays a vital role in the Windows ecosystem, serving as a critical tool for IT professionals to manage the distribution of updates released by Microsoft. WSUS enables administrators to deploy updates to Windows clients efficiently and effectively, ensuring that systems remain secure and operational. However, a significant security flaw, classified as CVE-2025-59287, has been recently reported that raises concerns about its integrity and the potential risks to systems utilizing this service.
The vulnerability in WSUS allows malicious actors to exploit its architecture, enabling unauthorized access to the server. This operation could lead to the deployment of compromised updates, which might subsequently compromise the security of connected systems. The nature of CVE-2025-59287 lies in its ability to manipulate update requests, potentially allowing hackers to insert malicious payloads into what would appear to be legitimate updates. Such an attack could have widespread implications, affecting numerous systems that rely on WSUS for critical updates.
This vulnerability was discovered by cybersecurity researchers who diligently monitor potential weaknesses in popular software infrastructures. Through a process of testing and analysis, they identified the anomaly within the WSUS framework, which prompted an immediate response from Microsoft. The swift patching of this security flaw underscores the essential nature of continual system updates and the robust measures that organizations must implement to protect against increasingly sophisticated threat actors.
By understanding the WSUS security flaw and the mechanics of its exploit, organizations can better comprehend the risks posed to their infrastructures. The repercussions of this vulnerability extend beyond mere operational disruptions; they could lead to data breaches or the deployment of ransomware, presenting a significant threat. Thus, it becomes imperative for organizations to actively monitor their systems and apply the latest security patches to safeguard against potential exploitation.
The Attack Methodology: How Shadowpad Malware Was Distributed
The distribution of the Shadowpad malware was executed through a sophisticated approach targeting Windows servers equipped with the Windows Server Update Services (WSUS). The attackers exploited a specific vulnerability identified as CVE-2025-59287, a critical flaw that allowed unauthorized access to these servers. Once they successfully gained entry, they leveraged a variety of tools and techniques to disseminate the malware across the compromised networks. This initial access was pivotal, as it opened the pathways for further exploitation.
Among the tools utilized by the attackers, PowerCat emerged as a significant asset. PowerCat is a PowerShell utility that enables network communication, particularly for exploiting and transferring files. By employing PowerCat, the attackers were able to create a reverse shell, which facilitated interactive sessions on the target systems. This capability allowed them to perform additional reconnaissance and extend their control over the network environment effectively. The versatility of PowerCat underscored the attackers’ proficiency in manipulating system vulnerabilities to achieve their objectives.
Furthermore, the procedural approach adopted by the attackers highlights a well-thought-out strategy. After exploiting CVE-2025-59287, they executed a series of commands that allowed them to configure and deploy the Shadowpad malware seamlessly. This malware was designed to remain hidden while exfiltrating sensitive information and performing actions aligned with the attackers’ intentions. The timeline of the attack showcased how quickly and efficiently the malware could proliferate through vulnerable systems once the initial access was secured.
By understanding the distribution methods utilized in the Shadowpad incident, organizations can better prepare for potential threats. Recognizing the exploitation of known vulnerabilities like CVE-2025-59287 is crucial in implementing effective security measures to prevent similar attacks in the future.
Impacts and Consequences of the Shadowpad Malware Distribution
The dissemination of Shadowpad malware has led to significant ramifications for various organizations across multiple sectors. One of the foremost concerns is the risk of data breaches, where sensitive information can be exfiltrated by malicious actors. Such breaches not only compromise client and company data but also lead to a breach of trust between organizations and their stakeholders. With the increasing reliance on digital infrastructures, any compromise can result in severe repercussions.
Financial losses represent another grim outcome of the Shadowpad malware incident. Organizations may incur substantial costs related to incident response, forensic investigations, and system recovery efforts. Moreover, the potential for regulatory fines, particularly for firms that fail to comply with data protection regulations, can exacerbate financial strain. As incidents stack up, organizations may also face a downturn in customer trust, which can culminate in decreased revenue and long-lasting economic damage.
Reputation damage is yet another crucial aspect that organizations must contend with post-incident. A malware attack signals weaknesses in an organization’s security policies and measures, which can lead to negative press coverage and loss of business. Trust is hard-earned, and once reputational damage occurs, it requires extensive and often costly efforts to rebuild. Organizations such as service providers, educational institutions, and healthcare facilities have been markedly impacted, wherein sensitive client data was compromised, resulting in public outcry and legal challenges.
Beyond the immediate effects on individual organizations, the Shadowpad incident has broader implications for the cybersecurity landscape. It underscores the critical nature of timely patching and updates. The evolving nature of cyber threats necessitates that organizations adopt proactive security measures and foster a culture of awareness regarding vulnerabilities. Occurrences like this highlight the need for continual education on security protocols and the importance of regular software updates to defend against emerging threats.
Preventative Measures and Recommendations for Security Best Practices
To mitigate risks associated with vulnerabilities such as the recent WSUS security flaw and similar incidents, organizations must adopt a proactive approach to cybersecurity. Proper configuration of Windows Server Update Services (WSUS) plays a vital role in securing their infrastructure. It is essential to restrict access to WSUS servers to only authorized personnel and to implement role-based access controls. This ensures that only users who require specific permissions to manage updates have access, minimizing the risk of unauthorized manipulation.
Regular patch management is another critical aspect of a robust cybersecurity framework. Organizations should establish a routine schedule for patching and updating all software components, including operating systems, applications, and third-party software. This process should incorporate automated updates where applicable, to ensure that newly discovered vulnerabilities are promptly addressed. Furthermore, maintaining an inventory of all devices and software within the organization can enhance visibility regarding what needs updates and help prioritize patching efforts based on the severity of vulnerabilities.
Utilizing advanced cybersecurity solutions is essential for bolstering an organization’s defenses against emerging threats. Implementing endpoint protection platforms (EPP), intrusion detection systems (IDS), and firewalls can help detect and prevent malicious activity from impacting the system. Additionally, deploying real-time monitoring solutions can facilitate immediate incident response, further strengthening an organization’s security posture.
Regular security audits, conducted by internal teams or third-party professionals, can identify potential gaps in security practices. These audits should assess the effectiveness of existing security measures and recommend improvements. Coupled with employee training on cybersecurity awareness, organizations can significantly reduce the risk of human error leading to security breaches. Training should cover best practices for recognizing phishing attempts and the importance of strong password policies. By implementing these strategies, organizations can navigate the evolving landscape of cybersecurity threats more effectively.
-

China-Linked APT31 Orchestrates Advanced Stealth Cyberattacks on Russian IT via Cloud Infrastructure
The advanced persistent threat (APT) group APT31, linked to China, has been identified as orchestrating sophisticated cyberattacks against the Russian information technology sector from 2024 to 2025. These campaigns have targeted companies serving as contractors and integrators for government agencies, utilizing cloud-based services to evade detection for extended periods. The technical complexity and persistence of these attacks underscore the evolving landscape of nation-state cyber operations.
-
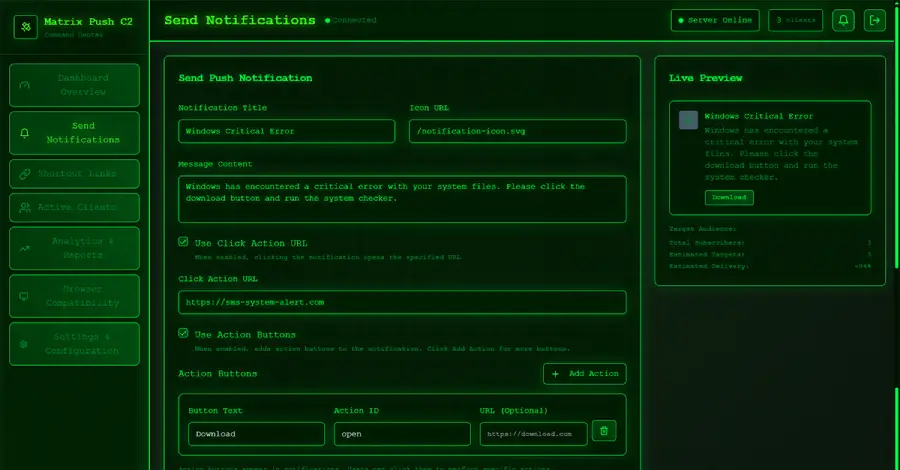
Matrix Push C2: Browser Notification Exploits Drive Fileless, Cross-Platform Phishing
Threat actors are increasingly leveraging browser notifications to facilitate phishing attacks through a new command-and-control (C2) platform, Matrix Push C2. This fileless, browser-native framework employs push notifications, deceptive alerts, and link redirects to deliver malicious payloads across multiple operating systems. Security researchers emphasize the cross-platform risk and the importance of robust browser security policies to mitigate these advanced attack vectors.
-

CISA Alerts to Active Exploitation of Oracle Identity Manager Critical Zero-Day (CVE-2025-61757)
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning regarding active exploitation of a critical vulnerability in Oracle Identity Manager, cataloged as CVE-2025-61757 (CVSS 9.8). This flaw, stemming from missing authentication for a critical function, allows pre-authenticated attackers to compromise affected systems. Organizations are strongly advised to apply available patches and review their identity management security posture.
-

Grafana Remediates CVSS 10.0 SCIM Vulnerability Enabling Privilege Escalation
Grafana has addressed a maximum severity vulnerability (CVE-2025-41115, CVSS 10.0) within its System for Cross-domain Identity Management (SCIM) component. This flaw could permit privilege escalation or user impersonation in certain deployment scenarios. Administrators are urged to update to the latest software version and review SCIM configurations to ensure organizational security.
