The Hacker NewsA previously undocumented threat activity cluster has been attributed to an ongoing malicious campaign targeting education and healthcare sectors in the U.S. since at least December 2025.
The campaign is being tracked by Cisco Talos under the moniker UAT-10027. The end goal of the attacks is to deliver a never-before-seen backdoor codenamed Dohdoor.
“Dohdoor utilizes the DNS-over-HTTPS (DoH)
Category: news
-

UAT-10027 Targets U.S. Education and Healthcare with Dohdoor Backdoor
-

ThreatsDay Bulletin: Kali Linux + Claude, Chrome Crash Traps, WinRAR Flaws, LockBit & 15+ Stories
The Hacker NewsNothing here looks dramatic at first glance. That’s the point. Many of this week’s threats begin with something ordinary, like an ad, a meeting invite, or a software update.
Behind the scenes, the tactics are sharper. Access happens faster. Control is established sooner. Cleanup becomes harder.
Here is a quick look at the signals worth paying attention to.AI-powered command
-

Expert Recommends: Prepare for PQC Right Now
The Hacker NewsIntroduction: Steal It Today, Break It in a Decade
Digital evolution is unstoppable, and though the pace may vary, things tend to fall into place sooner rather than later. That, of course, applies to adversaries as well. The rise of ransomware and cyber extortion generated funding for a complex and highly professional criminal ecosystem. The era of the cloud brought general availability of -
Microsoft Warns Developers of Fake Next.js Job Repos Delivering In-Memory Malware
The Hacker NewsA “coordinated developer-targeting campaign” is using malicious repositories disguised as legitimate Next.js projects and technical assessments to trick victims into executing them and establish persistent access to compromised machines.
“The activity aligns with a broader cluster of threats that use job-themed lures to blend into routine developer workflows and increase the likelihood of code -

Google Disrupts UNC2814 GRIDTIDE Campaign After 53 Breaches Across 42 Countries
The Hacker NewsGoogle on Wednesday disclosed that it worked with industry partners to disrupt the infrastructure of a suspected China-nexus cyber espionage group tracked as UNC2814 that breached at least 53 organizations across 42 countries.
“This prolific, elusive actor has a long history of targeting international governments and global telecommunications organizations across Africa, Asia, and the Americas,” -
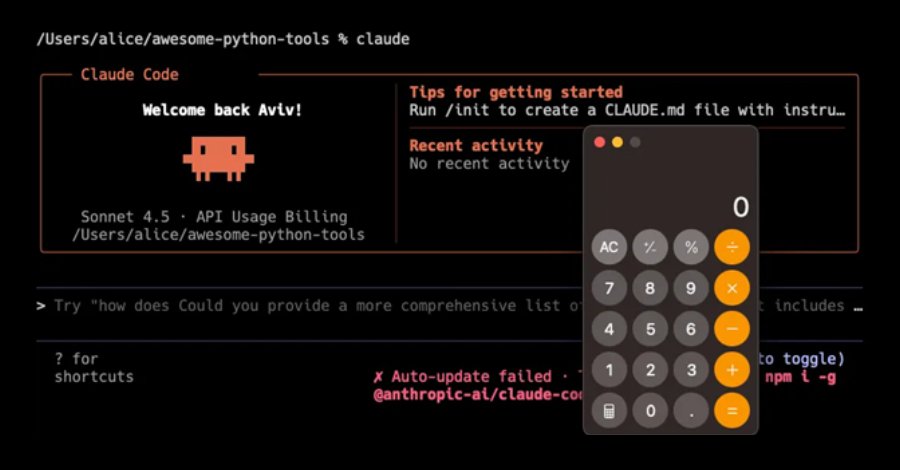
Claude Code Flaws Allow Remote Code Execution and API Key Exfiltration
The Hacker NewsCybersecurity researchers have disclosed multiple security vulnerabilities in Anthropic’s Claude Code, an artificial intelligence (AI)-powered coding assistant, that could result in remote code execution and theft of API credentials.
“The vulnerabilities exploit various configuration mechanisms, including Hooks, Model Context Protocol (MCP) servers, and environment variables – executing -

SLH Offers $500–$1,000 Per Call to Recruit Women for IT Help Desk Vishing Attacks
The Hacker NewsThe notorious cybercrime collective known as Scattered LAPSUS$ Hunters (SLH) has been observed offering financial incentives to recruit women to pull off social engineering attacks.
The idea is to hire them for voice phishing campaigns targeting IT help desks, Dataminr said in a new threat brief. The group is said to be offering anywhere between $500 and $1,000 upfront per call, in addition to -

Top 5 Ways Broken Triage Increases Business Risk Instead of Reducing It
The Hacker NewsTriage is supposed to make things simpler. In a lot of teams, it does the opposite.
When you can’t reach a confident verdict early, alerts turn into repeat checks, back-and-forth, and “just escalate it” calls. That cost doesn’t stay inside the SOC; it shows up as missed SLAs, higher cost per case, and more room for real threats to slip through.
So where does triage go wrong? Here are five triage -

Malicious NuGet Packages Stole ASP.NET Data; npm Package Dropped Malware
The Hacker NewsCybersecurity researchers have discovered four malicious NuGet packages that are designed to target ASP.NET web application developers to steal sensitive data.
The campaign, discovered by Socket, exfiltrates ASP.NET Identity data, including user accounts, role assignments, and permission mappings, as well as manipulates authorization rules to create persistent backdoors in victim applications. -

UAC-0050 Targets European Financial Institution With Spoofed Domain and RMS Malware
The Hacker NewsA Russia-aligned threat actor has been observed targeting a European financial institution as part of a social engineering attack to likely facilitate intelligence gathering or financial theft, signaling a possible expansion of the threat actor’s targeting beyond Ukraine and into entities supporting the war-torn nation.
The activity, which targeted an unnamed entity involved in regional