The Hacker NewsThe Problem: The Identities Left Behind
As organizations grow and evolve, employees, contractors, services, and systems come and go – but their accounts often remain. These abandoned or “orphan” accounts sit dormant across applications, platforms, assets, and cloud consoles.
The reason they persist isn’t negligence – it’s fragmentation.
Traditional IAM and IGA systems are designedRead More
Category: news
-

The Hidden Risk of Orphan Accounts
-
Filling the Most Common Gaps in Google Workspace Security
The Hacker NewsSecurity teams at agile, fast-growing companies often have the same mandate: secure the business without slowing it down. Most teams inherit a tech stack optimized for breakneck growth, not resilience. In these environments, the security team is the helpdesk, the compliance expert, and the incident response team all rolled into one.
Securing the cloud office in this scenario is all aboutRead More -
Critical GNU InetUtils telnetd Flaw Lets Attackers Bypass Login and Gain Root Access
The Hacker NewsA critical security flaw has been disclosed in the GNU InetUtils telnet daemon (telnetd) that went unnoticed for nearly 11 years.
The vulnerability, tracked as CVE-2026-24061, is rated 9.8 out of 10.0 on the CVSS scoring system. It affects all versions of GNU InetUtils from version 1.9.3 up to and including version 2.7.
“Telnetd in GNU Inetutils through 2.7 allows remote authentication bypassRead More -
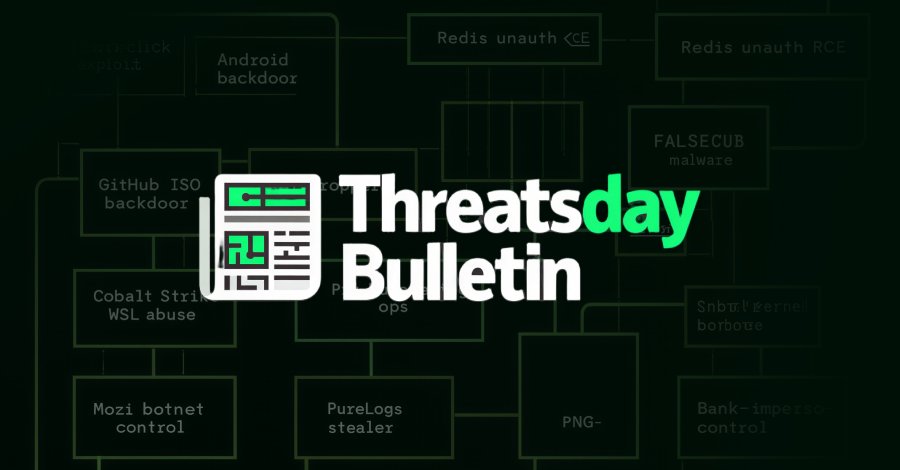
ThreatsDay Bulletin: Pixel Zero-Click, Redis RCE, China C2s, RAT Ads, Crypto Scams & 15+ Stories
The Hacker NewsMost of this week’s threats didn’t rely on new tricks. They relied on familiar systems behaving exactly as designed, just in the wrong hands. Ordinary files, routine services, and trusted workflows were enough to open doors without forcing them.
What stands out is how little friction attackers now need. Some activity focused on quiet reach and coverage, others on timing and reuse. The emphasisRead More -
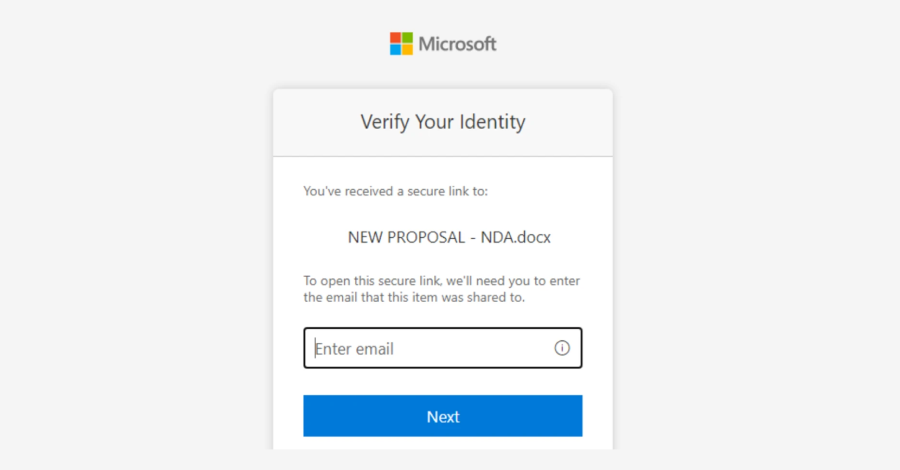
Microsoft Flags Multi-Stage AitM Phishing and BEC Attacks Targeting Energy Firms
The Hacker NewsMicrosoft has warned of a multi‑stage adversary‑in‑the‑middle (AitM) phishing and business email compromise (BEC) campaign targeting multiple organizations in the energy sector.
“The campaign abused SharePoint file‑sharing services to deliver phishing payloads and relied on inbox rule creation to maintain persistence and evade user awareness,” the Microsoft Defender Security Research Team said.Read More -

New Osiris Ransomware Emerges as New Strain Using POORTRY Driver in BYOVD Attack
The Hacker NewsCybersecurity researchers have disclosed details of a new ransomware family called Osiris that targeted a major food service franchisee operator in Southeast Asia in November 2025.
The attack leveraged a malicious driver called POORTRY as part of a known technique referred to as bring your own vulnerable driver (BYOVD) to disarm security software, the Symantec and Carbon Black Threat HunterRead More -

Fortinet Confirms Active FortiCloud SSO Bypass on Fully Patched FortiGate Firewalls
The Hacker NewsFortinet has officially confirmed that it’s working to completely plug a FortiCloud SSO authentication bypass vulnerability following reports of fresh exploitation activity on fully-patched firewalls.
“In the last 24 hours, we have identified a number of cases where the exploit was to a device that had been fully upgraded to the latest release at the time of the attack, which suggested a newRead More -

TikTok Forms U.S. Joint Venture to Continue Operations Under 2025 Executive Order
The Hacker NewsTikTok on Friday officially announced that it formed a joint venture that will allow the hugely popular video-sharing application to continue operating in the U.S.
The new venture, named TikTok USDS Joint Venture LLC, has been established in compliance with the Executive Order signed by U.S. President Donald Trump in September 2025, the platform said. The new deal will see TikTok’s ChineseRead More -
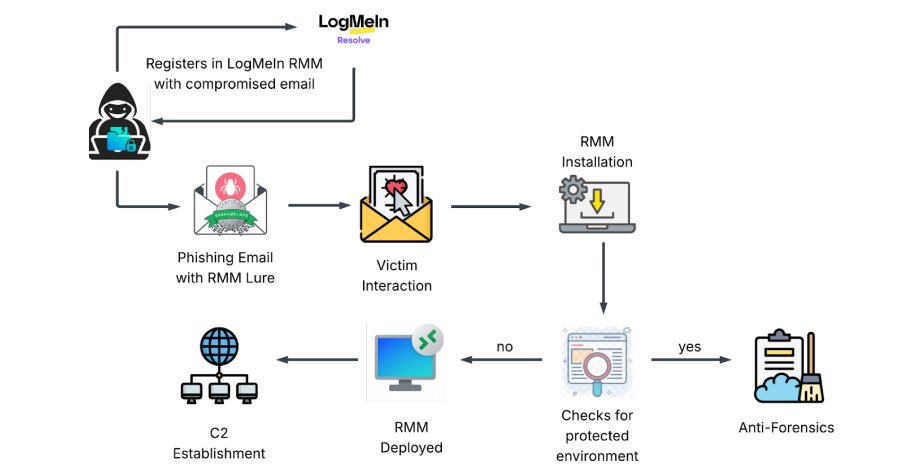
Phishing Attack Uses Stolen Credentials to Install LogMeIn RMM for Persistent Access
The Hacker NewsCybersecurity researchers have disclosed details of a new dual-vector campaign that leverages stolen credentials to deploy legitimate Remote Monitoring and Management (RMM) software for persistent remote access to compromised hosts.
“Instead of deploying custom viruses, attackers are bypassing security perimeters by weaponizing the necessary IT tools that administrators trust,” KnowBe4 ThreatRead More -
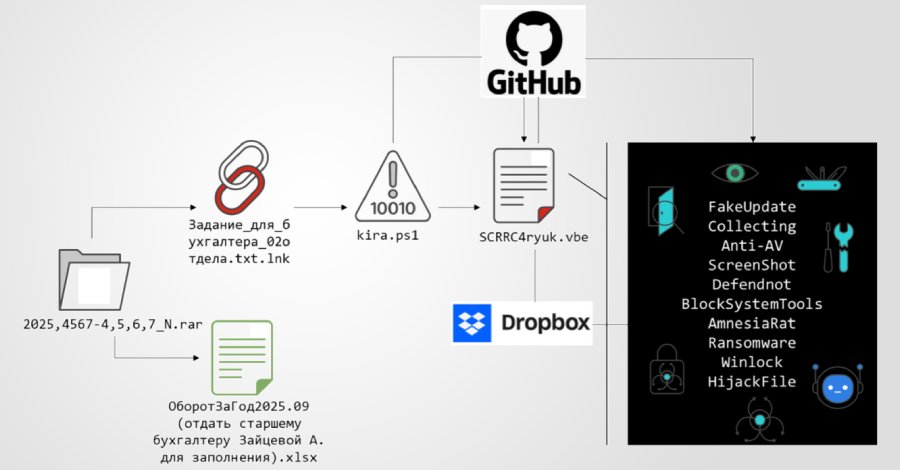
Multi-Stage Phishing Campaign Targets Russia with Amnesia RAT and Ransomware
The Hacker NewsA new multi-stage phishing campaign has been observed targeting users in Russia with ransomware and a remote access trojan called Amnesia RAT.
“The attack begins with social engineering lures delivered via business-themed documents crafted to appear routine and benign,” Fortinet FortiGuard Labs researcher Cara Lin said in a technical breakdown published this week. “These documents andRead More