The Hacker NewsThe Russian nation-state hacking group known as Sandworm has been attributed to what has been described as the “largest cyber attack” targeting Poland’s power system in the last week of December 2025.
The attack was unsuccessful, the country’s energy minister, Milosz Motyka, said last week.
“The command of the cyberspace forces has diagnosed in the last days of the year the strongest attack onRead More
Category: news
-

New DynoWiper Malware Used in Attempted Sandworm Attack on Polish Power Sector
-

Who Approved This Agent? Rethinking Access, Accountability, and Risk in the Age of AI Agents
The Hacker NewsAI agents are accelerating how work gets done. They schedule meetings, access data, trigger workflows, write code, and take action in real time, pushing productivity beyond human speed across the enterprise.
Then comes the moment every security team eventually hits:
“Wait… who approved this?”
Unlike users or applications, AI agents are often deployed quickly, shared broadly,Read More -

CISA Adds Actively Exploited VMware vCenter Flaw CVE-2024-37079 to KEV Catalog
The Hacker NewsThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added a critical security flaw affecting Broadcom VMware vCenter Server that was patched in June 2024 to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild.
The vulnerability in question is CVE-2024-37079 (CVSS score: 9.8), which refers to a heap overflow in theRead More -
Indian Users Targeted in Tax Phishing Campaign Delivering Blackmoon Malware
The Hacker NewsCybersecurity researchers have discovered an ongoing campaign that’s targeting Indian users with a multi-stage backdoor as part of a suspected cyber espionage campaign.
The activity, per the eSentire Threat Response Unit (TRU), involves using phishing emails impersonating the Income Tax Department of India to trick victims into downloading a malicious archive, ultimately granting the threatRead More -
Malicious VS Code AI Extensions with 1.5 Million Installs Steal Developer Source Code
The Hacker NewsCybersecurity researchers have discovered two malicious Microsoft Visual Studio Code (VS Code) extensions that are advertised as artificial intelligence (AI)-powered coding assistants, but also harbor covert functionality to siphon developer data to China-based servers.
The extensions, which have 1.5 million combined installs and are still available for download from the official Visual StudioRead More -

⚡ Weekly Recap: Firewall Flaws, AI-Built Malware, Browser Traps, Critical CVEs & More
The Hacker NewsSecurity failures rarely arrive loudly. They slip in through trusted tools, half-fixed problems, and habits people stop questioning. This week’s recap shows that pattern clearly.
Attackers are moving faster than defenses, mixing old tricks with new paths. “Patched” no longer means safe, and every day, software keeps becoming the entry point.
What follows is a set of small but telling signals.Read More -

Winning Against AI-Based Attacks Requires a Combined Defensive Approach
The Hacker NewsIf there’s a constant in cybersecurity, it’s that adversaries are always innovating. The rise of offensive AI is transforming attack strategies and making them harder to detect. Google’s Threat Intelligence Group, recently reported on adversaries using Large Language Models (LLMs) to both conceal code and generate malicious scripts on the fly, letting malware shape-shift in real-time to evadeRead More
-

Konni Hackers Deploy AI-Generated PowerShell Backdoor Against Blockchain Developers
The Hacker NewsThe North Korean threat actor known as Konni has been observed using PowerShell malware generated using artificial intelligence (AI) tools to target developers and engineering teams in the blockchain sector.
The phishing campaign has targeted Japan, Australia, and India, highlighting the adversary’s expansion of the targeting scope beyond South Korea, Russia, Ukraine, and European nations, CheckRead More -
Experts Detect Pakistan-Linked Cyber Campaigns Aimed at Indian Government Entities
The Hacker NewsIndian government entities have been targeted in two campaigns undertaken by a threat actor that operates in Pakistan using previously undocumented tradecraft.
The campaigns have been codenamed Gopher Strike and Sheet Attack by Zscaler ThreatLabz, which identified them in September 2025.
“While these campaigns share some similarities with the Pakistan-linked Advanced Persistent Threat (APT)Read More -
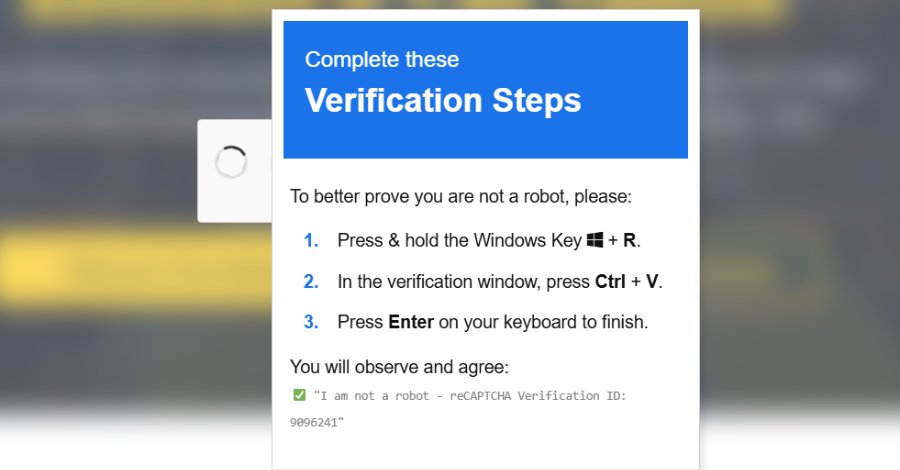
ClickFix Attacks Expand Using Fake CAPTCHAs, Microsoft Scripts, and Trusted Web Services
The Hacker NewsCybersecurity researchers have disclosed details of a new campaign that combines ClickFix-style fake CAPTCHAs with a signed Microsoft Application Virtualization (App-V) script to distribute an information stealer called Amatera.
“Instead of launching PowerShell directly, the attacker uses this script to control how execution begins and to avoid more common, easily recognized execution paths,”Read More