The Hacker NewsCybersecurity teams increasingly want to move beyond looking at threats and vulnerabilities in isolation. It’s not only about what could go wrong (vulnerabilities) or who might attack (threats), but where they intersect in your actual environment to create real, exploitable exposure.
Which exposures truly matter? Can attackers exploit them? Are our defenses effective?
Continuous Threat ExposureRead More
Category: news
-
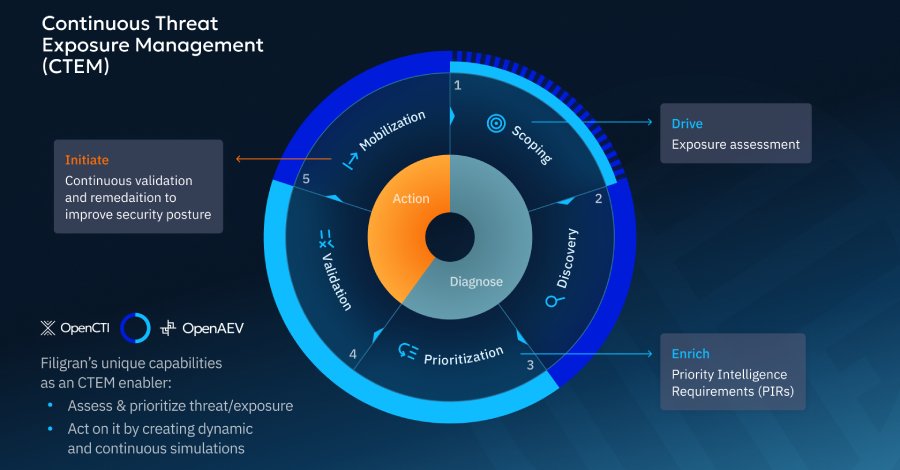
CTEM in Practice: Prioritization, Validation, and Outcomes That Matter
-

CISA Updates KEV Catalog with Four Actively Exploited Software Vulnerabilities
The Hacker NewsThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added four security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild.
The list of vulnerabilities is as follows –CVE-2025-68645 (CVSS score: 8.8) – A PHP remote file inclusion vulnerability in Synacor Zimbra Collaboration Suite (ZCS) that could allow aRead More
-

From Triage to Threat Hunts: How AI Accelerates SecOps
The Hacker NewsIf you work in security operations, the concept of the AI SOC agent is likely familiar. Early narratives promised total autonomy. Vendors seized on the idea of the “Autonomous SOC” and suggested a future where algorithms replaced analysts.
That future has not arrived. We have not seen mass layoffs or empty security operations centers. We have instead seen the emergence of a practical reality.Read More -

Critical vm2 Node.js Flaw Allows Sandbox Escape and Arbitrary Code Execution
The Hacker NewsA critical sandbox escape vulnerability has been disclosed in the popular vm2 Node.js library that, if successfully exploited, could allow attackers to run arbitrary code on the underlying operating system.
The vulnerability, tracked as CVE-2026-22709, carries a CVSS score of 9.8 out of 10.0 on the CVSS scoring system.
“In vm2 for version 3.10.0, Promise.prototype.then Promise.prototype.catchRead More -

Two Ivanti EPMM Zero-Day RCE Flaws Actively Exploited, Security Updates Released
The Hacker NewsIvanti has rolled out security updates to address two security flaws impacting Ivanti Endpoint Manager Mobile (EPMM) that have been exploited in zero-day attacks, one of which has been added by the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to its Known Exploited Vulnerabilities (KEV) catalog.
The critical-severity vulnerabilities are listed below –CVE-2026-1281 (CVSS score:Read More
-
Researchers Find 175,000 Publicly Exposed Ollama AI Servers Across 130 Countries
The Hacker NewsA new joint investigation by SentinelOne SentinelLABS, and Censys has revealed that the open-source artificial intelligence (AI) deployment has created a vast “unmanaged, publicly accessible layer of AI compute infrastructure” that spans 175,000 unique Ollama hosts across 130 countries.
These systems, which span both cloud and residential networks across the world, operate outside theRead More -

ThreatsDay Bulletin: New RCEs, Darknet Busts, Kernel Bugs & 25+ More Stories
The Hacker NewsThis week’s updates show how small changes can create real problems. Not loud incidents, but quiet shifts that are easy to miss until they add up. The kind that affects systems people rely on every day.
Many of the stories point to the same trend: familiar tools being used in unexpected ways. Security controls are being worked on. Trusted platforms turning into weak spots. What looks routine onRead More -

Survey of 100+ Energy Systems Reveals Critical OT Cybersecurity Gaps
The Hacker NewsA study by OMICRON has revealed widespread cybersecurity gaps in the operational technology (OT) networks of substations, power plants, and control centers worldwide. Drawing on data from more than 100 installations, the analysis highlights recurring technical, organizational, and functional issues that leave critical energy infrastructure vulnerable to cyber threats.
The findings are based onRead More -

3 Decisions CISOs Need to Make to Prevent Downtime Risk in 2026
The Hacker NewsBeyond the direct impact of cyberattacks, enterprises suffer from a secondary but potentially even more costly risk: operational downtime, any amount of which translates into very real damage. That’s why for CISOs, it’s key to prioritize decisions that reduce dwell time and protect their company from risk.
Three strategic steps you can take this year for better results:
1. Focus on today’sRead More -
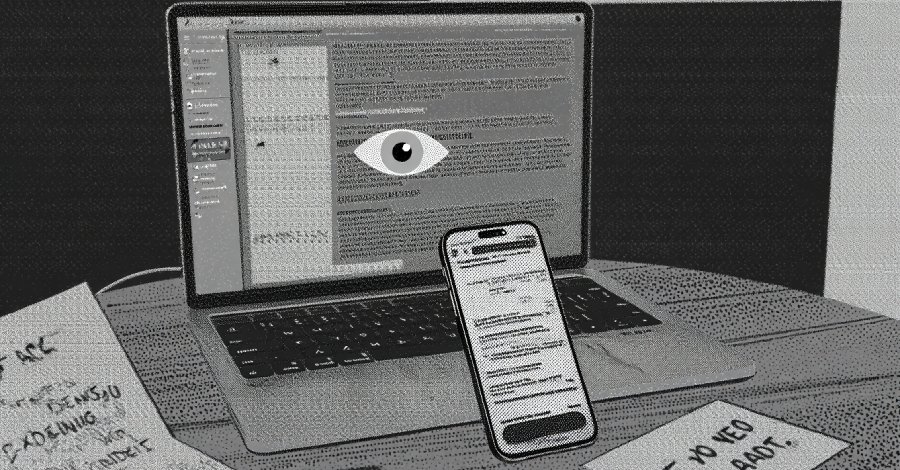
Iran-Linked RedKitten Cyber Campaign Targets Human Rights NGOs and Activists
The Hacker NewsA Farsi-speaking threat actor aligned with Iranian state interests is suspected to be behind a new campaign targeting non-governmental organizations and individuals involved in documenting recent human rights abuses.
The activity, observed by HarfangLab in January 2026, has been codenamed RedKitten. It’s said to coincide with the nationwide unrest in Iran that began towards the end of 2025,Read More